
Data security and data privacy are still becoming more and more important. On the flip side of trying to tighten the security layer is that security is becoming vastly harder to manage.
VMware’s vision about security is that it has to be easy to manage. This of course applies to traditional applications as well as cloud native apps, such as VMware’s Photon. Of course in both cases it is mandatory that the infrastructure hosting data, the data itself and the access to data would be always as secure as possible.

vSphere 6.5 Enhanced Logging
For years we have been having issues getting the right logs for auditing out of vCenter and ESXi server logs. For example today, vSphere 5.x and vSphere 6.x logs will show you who made a change to what VM, but will not show you exactly what has been changed. Well in vSphere 6.5 you will be able to see the who, what, where and when. As such vSphere 6.5 opens the gates to decent auditing logs. To make that happen the vCenter events will be exposed through a syslog server. This allows us to have better access to the vCenter logs without having to turn on verbose logging and this will give us better auditing options:
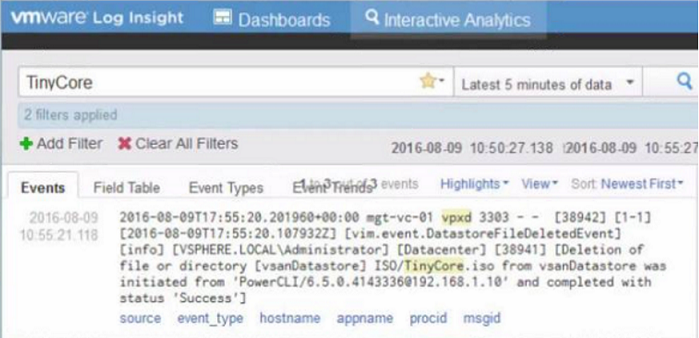
Here is an example where VMware uses Log Insight as a syslog server to show the enhanced logging capabilities of vSphere 6.5:
You can see:
- What datastore the VM sits on
- By whom the change was made
- Using which tool : PowerCLI
- When the change was made
This post is part of a VMWorld Barcelona early access series:
What is new with VMware?
What is new in vSphere 6.5?
What is new in vSphere 6.5 HA/DRS and VSAN 6.5?
What is new in vSphere 6.5 Security?
What is new for Photon 1.1?
VM Encryption
One of the difficulties when you deal with encrypting systems is that you would have to monitor each and every encrypted system unless you have a decent management and monitor system.
To deal with these potential issues, VMware leverages the storage policies to apply an encryption policy to the VM you want to encrypt. A default encryption policy will be offered, which when applied will assign a key from the default key manager to that VM which will be used to encrypt the disk and virtual machine files. Take note that the files within the OS will not be encrypted.
The advantages of VM encryption are:
- Encrypts both the VMDK’s as the VM files
- Once the VM is encrypted all IO from the virtual scsi device for that VM will go through the encryption module before it hits the storage modules on the host. So all IO coming out of the VM will be encrypted.
- VM Guest OS agnostic
- Applied at the datastore level
- Hardware version agnostic
- Policy driven
- The guest OS has no access to the encryption keys
- Encrypted vMotion: If the VM is encrypted, so is the vMotion
So how does VM encryption work?
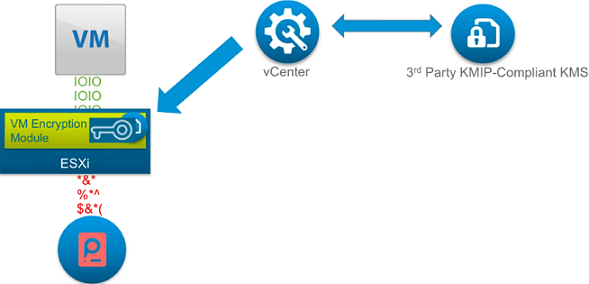
- When you apply the encryption storage policy to a VM, the VMDK’s of that VM will be encrypted.
To do that you of course need a key pair. One key for the VM and a root CA on the Key manager server.Mike Foley just send me a correction: No CA or Key pair is being used. ESXi will create the VM encryption key and that key is encrypted with the KMS key.
For sure you will have many questions about this exciting new security feature. May I suggest that you watch the VMworld Barcelona presentation about the new vSphere 6.5 security features once it is available? Mike Foley – vSphere Platform Security [INF8850].
Encrypted vMotion:
Encrypted vMotion means the data will be encrypted but not the vMotion network. There will be no specific encrypted VMotion network!
In case you want to vMotion a VM encrypted, you will have to set a specific setting in your VM which is possible from the vSphere webclient. Both hosts have to support this and if only one hosts supports this a normal vMotion will happen.
Secure boot for ESXi hosts and VM’s:
If you ever needed a way to make sure that your ESXi hosts can boot up cryptographically secure, VMware has found a way to make that happen by using the signed vib technology. Keep your ears open for this during Mike’s presentation, the solution is remarkably easy!
For the VM’s this will be a setting in the VM.

Leave a Reply